Between 2017 and 2023, North Korean hackers stole $3 billion in cryptocurrency. That’s not a typo. That’s more than the GDP of some small countries. And in February 2025, they pulled off a single heist worth $1.5 billion - the largest crypto theft in history. This isn’t random hacking. It’s state-funded warfare, disguised as code.
These aren’t lone teenagers in basements. This is a well-funded, highly organized operation run by North Korea’s military intelligence units. Groups like Lazarus, TraderTraitor, and Slow Pisces have spent years refining their tools, tactics, and timing. They don’t brute-force their way in. They wait. They watch. They trick.
How They Trick People, Not Systems
Crypto exchanges and wallets are built on strong encryption. Breaking them directly? Nearly impossible. So North Korean hackers don’t try. Instead, they target the humans who manage them.
In May 2024, they stole $308 million from DMM, a Japanese crypto platform. How? They didn’t crack a server. They sent a fake job offer on LinkedIn to an employee at Ginco - a company that builds wallet software for businesses. The victim downloaded a Python script labeled as a "pre-employment test." It was malware. Once installed, it stole session cookies. That’s like copying your house key while you’re asleep.
Within weeks, the hackers were impersonating that employee inside Ginco’s internal system. They watched how real transactions were approved. Then, when a DMM employee submitted a legitimate transfer request, the hackers quietly changed the destination address. The transaction went through. $308 million vanished.
This isn’t an exception. It’s the standard playbook. North Korean hackers use LinkedIn, Upwork, and even fake tech forums to find employees with access to crypto systems. They build trust over weeks. They send fake documents. They use Zoom calls to appear legitimate. Then, they strike.
The $1.5 Billion Bybit Heist
The February 2025 attack on Bybit changed everything. The hackers stole nearly $1.5 billion in Ether. That’s more than the total amount stolen in all 47 crypto heists of 2024 combined.
Chainalysis, the leading blockchain analytics firm, confirmed the funds were moved through decentralized exchanges and cross-chain bridges. These tools let hackers swap one cryptocurrency for another without going through regulated platforms. It’s like laundering cash through dozens of ATMs in different countries - each one obscuring the trail a little more.
Bybit didn’t get hacked because of weak security. They had multi-signature wallets, cold storage, and audits. But no system is safe if the person approving the transaction is compromised. The hackers didn’t need to break into Bybit’s servers. They just needed to trick one person into clicking a link.

Why This Is Worse Than Regular Cybercrime
Most crypto thieves want to vanish. North Korean hackers want to survive.
They’re not stealing to buy Lamborghinis. They’re stealing to fund nuclear missiles.
According to UN reports from December 2024, Pyongyang uses stolen crypto to buy materials for weapons programs. Sanctions have cut off their oil, cash, and trade. Crypto is their lifeline. That’s why they’ve increased attacks every year. In 2023, they stole $660 million. In 2024, it jumped to $1.34 billion. That’s a 103% increase.
They’re also smarter than other criminal groups. In 2024, North Korean groups accounted for 61% of all stolen crypto - even though they only carried out 20% of the attacks. That means each operation is bigger, better planned, and more profitable.
Other hackers get lucky. North Korea plans for years.
What’s Being Done About It?
The FBI, Japan’s National Police Agency, and the U.S. Department of Defense have been tracking these attacks since 2019. They’ve publicly named the hacker groups. They’ve frozen wallets. They’ve pressured exchanges to improve monitoring.
But it’s like trying to stop a river with a bucket. Every time they shut down one laundering route, North Korea finds another. They’ve learned to use DeFi protocols, privacy coins, and non-custodial wallets to hide their tracks.
Some exchanges have started using AI-powered monitoring tools that flag unusual wallet movements. Others now require dual approval for all large transfers - even internal ones. A few have started training employees like they’re in a military security drill: mock phishing tests, fake job offers, simulated breaches.
But most platforms still treat security as a checkbox. They update their firewall. They hire a consultant. They think they’re safe.
They’re not.
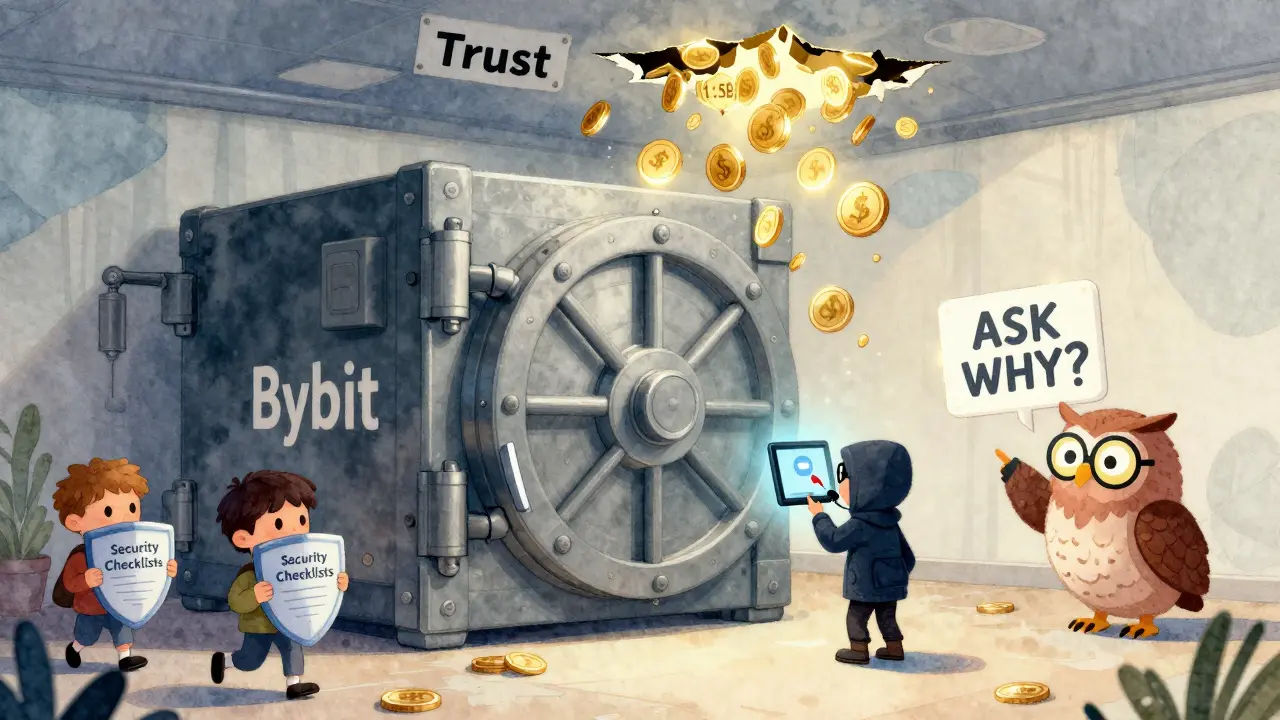
The Real Vulnerability Isn’t Tech - It’s Trust
The biggest flaw in crypto security today isn’t outdated software. It’s blind trust.
Companies assume their employees are safe because they’re "internal." They assume their wallet providers are trustworthy because they’ve been around for years. They assume audits mean security.
North Korean hackers exploit all of that.
They don’t need to break into a system. They just need someone to believe a stranger on LinkedIn.
That’s why the best defense isn’t more encryption. It’s skepticism.
Every employee should be trained to ask: "Why am I being asked to download this?" "Who really sent this message?" "What happens if I say no?"
Platforms need to stop treating security like a one-time setup. It’s a daily habit. It’s a culture. It’s asking questions before clicking.
What Happens Next?
The $1.5 billion Bybit theft didn’t scare North Korea. It energized them.
With sanctions tightening and traditional funding drying up, crypto theft is now their primary revenue stream. Experts believe 2025 will see even larger attacks - possibly targeting centralized exchanges in the U.S., South Korea, or Europe.
Some analysts predict North Korea will start hacking institutional investors - hedge funds, pension funds, even government crypto reserves. These targets have more money, less scrutiny, and often weaker employee training.
Meanwhile, regulators are scrambling. The U.S. Treasury has added over 150 crypto addresses linked to Lazarus to its sanctions list. The EU is drafting new rules requiring all exchanges to report suspicious activity within 24 hours.
But rules won’t stop a hacker who’s already inside your system.
Only vigilance will.
How did North Korea steal $3 billion in crypto?
North Korea used state-sponsored hacker groups like Lazarus and TraderTraitor to carry out over 58 cyberattacks between 2017 and 2023. They didn’t break into systems directly. Instead, they targeted employees through social engineering - fake job offers on LinkedIn, malicious files disguised as tests, and long-term infiltration. Once inside, they stole login credentials, manipulated transactions, and laundered funds across decentralized exchanges.
Is cryptocurrency itself unsafe?
No. The blockchain technology behind crypto is secure. The problem isn’t the code - it’s the people who use it. Most thefts happen because employees are tricked into giving up access, not because hackers cracked encryption. Even the most secure wallets can be bypassed if someone inside is fooled.
Why do North Korean hackers keep succeeding?
They have unlimited funding, patience, and a clear mission: fund weapons programs. They spend months building trust with targets, often using real professional profiles and fake company websites. They don’t rush. They wait for the perfect moment - like when an employee is approving a large transfer. Most companies don’t train staff to question unusual requests, making them easy targets.
Can blockchain analysis stop these thefts?
Yes, but only after the fact. Firms like Chainalysis and TRM Labs can trace stolen funds and identify wallet patterns linked to North Korean groups. But by the time they do, the money is already converted into Bitcoin, mixed through DeFi platforms, or moved across borders. Tracking doesn’t prevent theft - it just helps with attribution and occasional recovery.
What should crypto companies do to protect themselves?
Stop assuming internal systems are safe. Train every employee like they’re a frontline soldier - run monthly phishing simulations, require dual approval for all transfers, and limit access to only what’s necessary. Use blockchain monitoring tools that flag unusual movements. And never trust a file or link sent through a job application process - no matter how professional it looks.

